Mythos Just Rewrote the Rules of Cybersecurity: One AI Found 271 Firefox Vulnerabilities in a Month — More Than Human Teams Had in 18 Months
In early April 2026, Anthropic quietly released a preview of its new frontier model, Claude Mythos. Within weeks, the model had done something extraordinary: it discovered 271 previously unknown security vulnerabilities in Mozilla Firefox — a haul that dwarfs what human auditors and traditional fuzzing had uncovered over the previous year and a half.

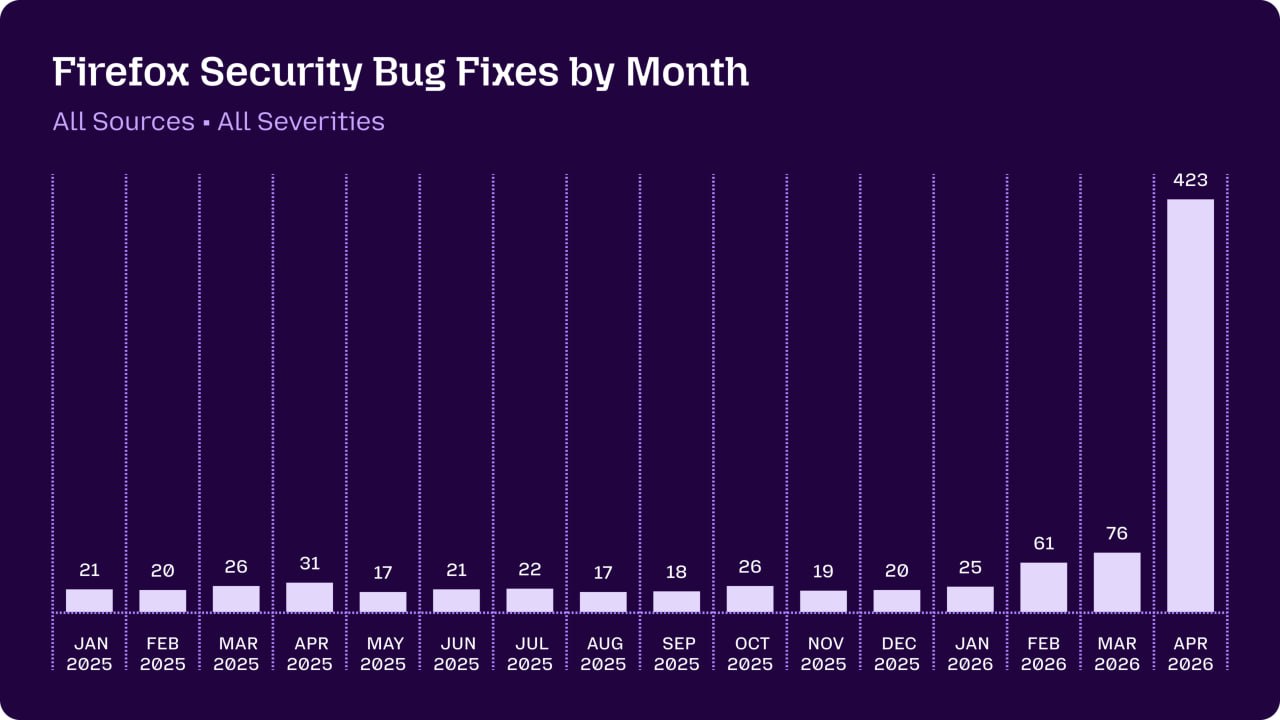
Then Mythos arrived. In a single evaluation run, it identified 271 issues — 180 of them rated sec-high, 80 sec-moderate, and 11 sec-low. These were fixed across Firefox 150 and the rapid point releases 149.0.2, 150.0.1, and 150.0.2, contributing to a total of 423 security bugs patched in April alone.
Mozilla’s detailed follow-up post on May 7, 2026 (“Behind the Scenes: Hardening Firefox with Claude Mythos Preview”) confirms the scale and the method. The team built a custom agentic harness on top of their existing fuzzing infrastructure. Mythos didn’t just scan code — it generated reproducible proof-of-concept test cases, reasoned over complex multiprocess browser architecture, patched the source in isolated VMs to test exploits, and produced reports with near-zero false positives.
The most alarming discoveries were sandbox escape bugs.
Several of the vulnerabilities allowed a compromised content process (the sandboxed part of the browser that renders web pages) to break out and reach the privileged parent process.

- A race condition over IPC that triggered use-after-free in IndexedDB.
- Malformed objects passed across process boundaries that could be deserialized into fake pointers in the parent.
- Refcount manipulation via WebTransport certificate floods.
- Gaps in RLBox sandboxing for third-party libraries.
On their own, these were dangerous. Chained with an initial content-process compromise (the kind that could come from a malicious website), they could enable full arbitrary code execution — potentially turning a simple link click into a complete system compromise. In other words: drive-by infection, no user interaction beyond visiting a page.
The fixes shipped fast. Three specific CVEs were publicly credited to Anthropic’s Frontier Red Team from earlier work, but the bulk of the 271 bugs rolled up under broader security advisories in Firefox 150.

Mozilla’s CTO and the security team described the experience as “vertigo-inducing.” For the first time, the defenders had a tool that could systematically surface latent bugs faster than attackers could weaponize them. As one internal summary put it: “Suddenly, the bugs are very good.”
This was exactly what Anthropic warned about when they announced Mythos Preview in April 2026. The model wasn’t trained specifically as a hacker — its offensive capabilities emerged as a side effect of superior general reasoning and code understanding. Early access was deliberately limited (via Project Glasswing) to responsible organizations so they could patch before the model became more widely available. Mozilla’s real-world deployment is the first large-scale public confirmation that the hype was not marketing fluff.
Cybersecurity has changed forever.

The internet just got a little safer — but only because defenders got there first.
Mozilla has already shipped the most secure Firefox in history. Other projects are watching closely. The message from the Mozilla team is clear and urgent: anyone building software today can (and should) start using modern models and harnesses to harden their code immediately. The opportunity is here. The peril is real. The race has begun.
Also read:
- AI Slop: The Glowing Pickle of Our Time
- David Zaslav Calls HBO Max Warner Bros. Discovery’s “Most Important Asset”
- Claude Mythos Just Broke Cybersecurity: The AI That Finds Vulnerabilities Better Than Most Human Hackers
- Japan: The World’s Must-Visit Destination in 2025
Thank you!