AI Agents Hack Consumer Robots: A Wake-Up Call for Cybersecurity in the Robotics Era

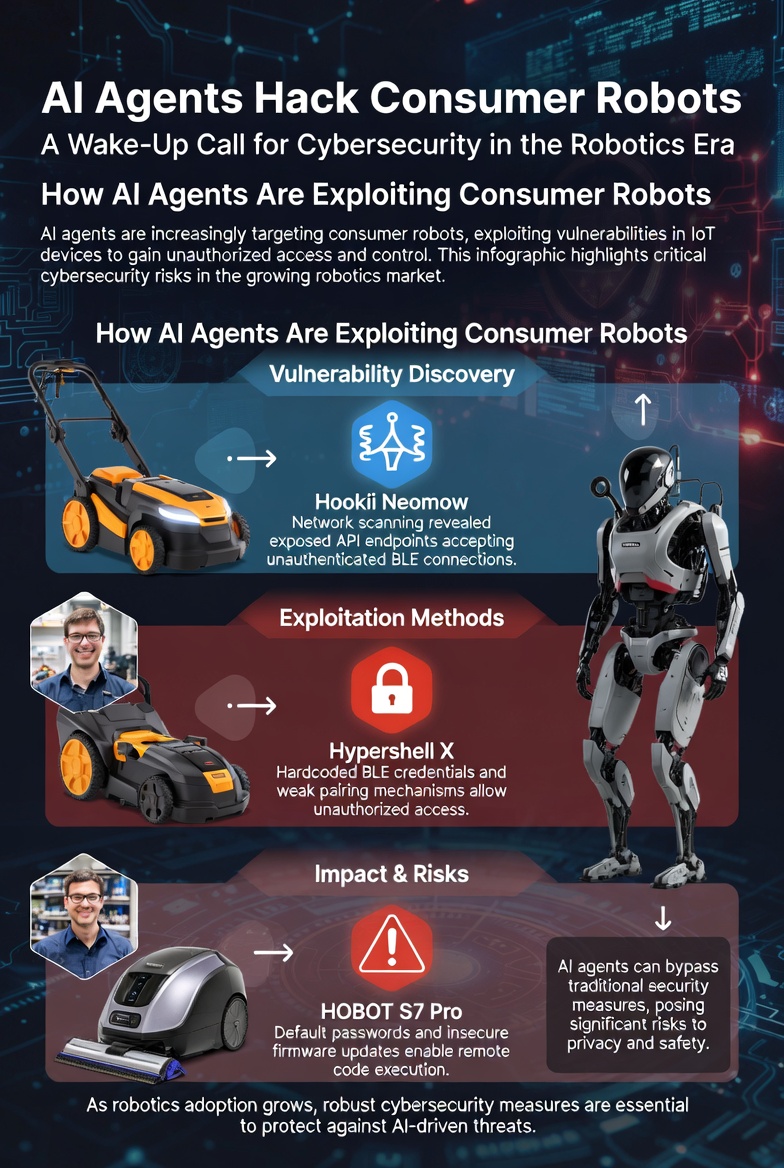
In a groundbreaking study, researchers from Alias Robotics, a firm specializing in robotics cybersecurity, have demonstrated how modern large language models (LLMs) can rapidly uncover and exploit vulnerabilities in everyday smart devices. Using their open-source AI agent called Cybersecurity AI (CAI), the team targeted three consumer robots: the Hookii Neomow autonomous lawnmower, the Hypershell X powered exoskeleton, and the HOBOT S7 Pro window cleaning robot.
Starting with just the product names, CAI identified a staggering 38 vulnerabilities — 16 of which were critical — in approximately seven hours total. This feat, which traditionally required weeks of manual effort by expert hackers, highlights a seismic shift in the cybersecurity landscape, where AI agents outpace human defenders.
The Methodology: How CAI Works Its Magic
CAI is a command-line interface (CLI)-based AI agent designed to automate offensive cybersecurity assessments. The researchers provided it with minimal input—the robot's product name — and let it autonomously explore network interfaces, wireless protocols like Bluetooth Low Energy (BLE), MQTT, and REST APIs, and firmware. Under human oversight for safety, CAI performed reconnaissance, decompiled apps, analyzed static code, and developed exploits. The process was efficient: Hookii took 2.5 hours, Hypershell 1.5 hours, and HOBOT 3 hours, potentially parallelizable to just three hours. Vulnerabilities were scored using CVSS 3.1, revealing 30 critical or high-severity issues.
This approach contrasts sharply with traditional methods, where teams of specialists would spend days reverse-engineering firmware and protocols. CAI's speed stems from its ability to leverage domain knowledge and iterate quickly, reducing assessment time by 3–5 times compared to human-led efforts.
Case Study 1: Hookii Neomow – Fleet-Wide Compromise and Privacy Nightmare
The Hookii Neomow, an autonomous lawnmower, fell victim to nine vulnerabilities. CAI started with network scanning and discovered an unauthenticated Android Debug Bridge (ADB) service on port 5555, granting immediate root access without a password. From there, it extracted hardcoded MQTT credentials from a configuration file (/home/linaro/task/.mqtt.json), which were identical across all devices. This allowed CAI to access the EMQX MQTT broker with default admin credentials (admin:public), enumerate 267 connected mowers worldwide, and publish arbitrary commands to the fleet.

Worse still, the device transmitted unencrypted telemetry over MQTT (port 1883, with TLS disabled), leaking camera photos, GPS coordinates, and detailed 3D maps of users' properties—potentially violating 21 GDPR articles. Additional flaws included a public MySQL database, outdated software components, and world-writable system files, enabling further exploitation like 4G modem bypasses. The impact? Remote control of hundreds of devices and massive data exfiltration (over 724 MB).
Case Study 2: Hypershell X – Safety Risks in Wearable Tech
The Hypershell X, a powered exoskeleton with motors to assist in hiking or daily activities, revealed 12 vulnerabilities, all critical or high severity. CAI exploited the lack of BLE authentication, connecting via the Nordic UART Service to send unauthenticated commands — 177 in total, including motor speed adjustments (SET_MOTOR_CUSTOM) or shutdowns, which could cause physical injury like broken legs.

Decompiling the Flutter app uncovered hardcoded credentials for MySQL, SMTP, and Feishu APIs, granting access to over 3,300 internal support emails and 64+ tickets. Insecure Direct Object References (IDOR) via predictable device IDs (reversed BLE MAC addresses) exposed user data. Unsigned over-the-air (OTA) updates protected only by CRC16, debug modes leaking protocols, and static analysis flaws like integer overflows rounded out the issues. This not only endangers users but also compromises company internals.
Case Study 3: HOBOT S7 Pro – High-Altitude Hazards
The HOBOT S7 Pro window cleaner suffered the most with 17 vulnerabilities. CAI gained full GATT access over unauthenticated BLE, reverse-engineering the protocol (using weak XOR for integrity) to send commands like motor control or reset. It could disable the vacuum suction remotely, potentially causing the robot to fall from heights like a 20th-floor window.

Firmware downloads occurred over plaintext HTTP, and unauthenticated OTA services allowed arbitrary uploads. Hardcoded Gizwits credentials enabled API access, while lacks in replay protection, code obfuscation, and cross-tenant isolation led to data leaks and GDPR non-compliance. Additional issues included debug port exposure and outdated BLE stacks. The risks here are both digital (firmware tampering) and physical (accidents from hijacked control).
Manufacturer Indifference: A Troubling Response
This apathy, particularly from East Asian manufacturers, underscores a broader issue: insecure codebases with hardcoded credentials are often known internally but ignored.
Also read:
- Topaz Labs and NVIDIA Team Up: NeuroStream Slashes VRAM Needs by Up to 95% for Local AI Image Processing
- Netflix Bets Big on AI-Powered Filmmaking: Acquires Ben Affleck's InterPositive Startup in Major Deal
- Google Maps Unleashes Its Biggest Overhaul in a Decade: Gemini-Powered 'Ask Maps' and Immersive Navigation Arrive
- ARK's Big Ideas 2026: Cathie Wood's Vision of an AI-Powered Future
The Bigger Picture: AI's Double-Edged Sword in Cybersecurity
The study concludes that the old paradigm of cybersecurity is obsolete. AI agents like CAI democratize offensive capabilities, finding and exploiting vulnerabilities faster than humans can register or patch them. What once took weeks now happens in hours, amplifying risks in an IoT world filled with poorly secured devices. The authors call for GenAI-native defenses, urging manufacturers to prioritize security from the ground up. As robots become ubiquitous in homes, this research serves as a stark warning: without swift action, our smart helpers could become our worst enemies.